If you walked the floor at RSAC this year, you probably noticed something odd.
Every booth still had “Zero Trust” plastered across it like a motivational poster from 2014, but the conversations happening inside those booths told a very different story.
The industry has quietly moved on.
Zero Trust, as it’s been marketed for the last decade, has officially entered its “participation trophy” era. Not because the concept failed, but because the implementation was built for a world that no longer exists. Attackers aren’t battering down firewalls anymore. They’re logging in, stealing tokens, hijacking sessions, and using GenAI to craft phishing emails more polished than your last board deck.
And yet, for years, we’ve treated a successful login like a sacred oath.
You authenticate once at 9:00 AM and the system basically says, “Great, you’re good forever.” In 2026, that’s the cybersecurity equivalent of TSA checking your ID once and saying, “Cool, you’re cleared for the rest of the month. Enjoy the airport.”
RSAC’s Quiet Admission: The Login Is Dead
The real story at RSAC wasn’t the flashy booths or the buzzwords. It was the subtle shift in how vendors talked about identity. Zero Trust Network Access wasn’t the star of the show anymore. Instead, we heard about:
- Continuous Adaptive Trust: Real‑time risk scoring that re‑evaluates you after every click.
- AI‑Driven Session Scoring: Detecting anomalies in how you interact with data in milliseconds.
- Behavioral Baselines: Increasingly using behavioral signals (and in some cases biometrics) to ensure the person who logged in at 9:00 AM is still the one at the keyboard at 2:00 PM.
Translation:
“That initial login? Yeah… it doesn’t mean anything anymore.”
Identity is no longer a static event. It’s a constantly shifting signal that needs to be re‑evaluated every time a user blinks, clicks, or does something even slightly off.
And here’s where the networking angle becomes impossible to ignore: identity is becoming a network‑level signal. You can’t score risk in milliseconds if your underlying connectivity is dropping packets like confetti. Continuous trust requires continuous telemetry, and that’s a network problem as much as a security one.
The perimeter didn’t disappear. It just shrunk down to the millisecond.
And with AI now capable of mimicking user behavior, “trust” itself becomes a liability.
The One Group That Looked Ready: Data Resilience
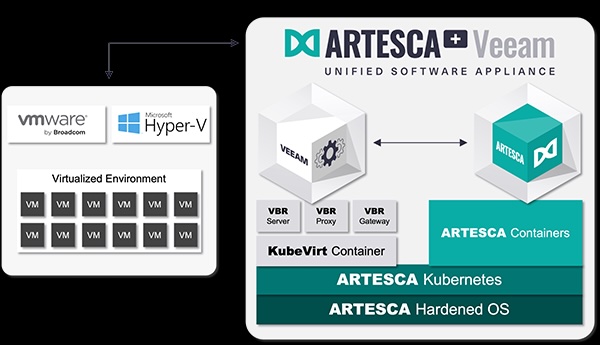
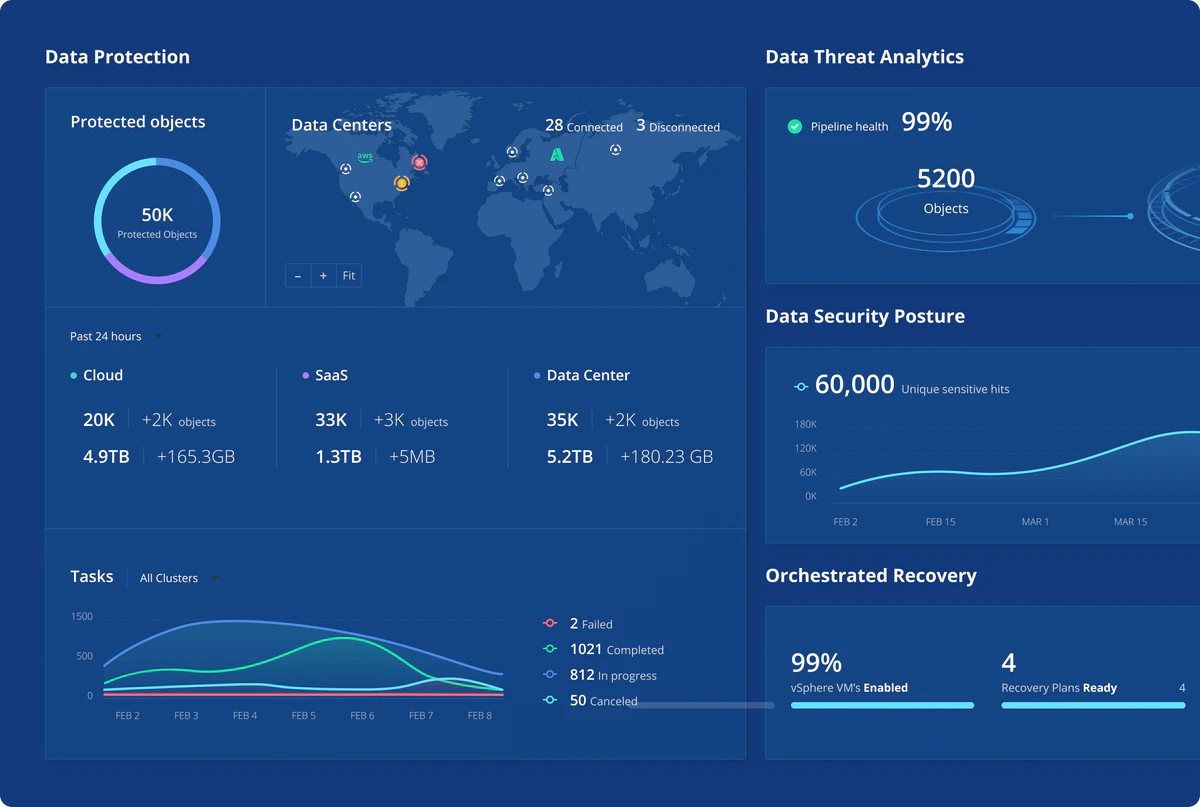
While most vendors were busy rebranding Zero Trust with new adjectives, the data‑resilience crowd seemed oddly calm. Veeam, in particular, leaned into a message that felt refreshingly grounded: If identity is volatile, your data better not be.
Because when sessions get hijacked, and they will, the only thing standing between you and a very bad day is clean, immutable recovery. Identity is now the first line of attack. Recovery is the last line of defense.
And here’s the networking tie‑in security folks don’t always say out loud: Immutable backups don’t matter if your east‑west traffic is a flat, high‑speed highway for lateral movement.
Network integrity is now a security primitive.
The Real RSAC Theme: Zero Assumption
If there was a unifying thread across the conference, it was this:
- Identity can’t be a one‑time event.
- Credentials should be assumed compromised.
- Sessions should be assumed volatile.
- AI is now part of both the attack surface and the defense stack.
- And none of this works without networks that are observable, deterministic, and resilient.
Zero Trust isn’t dead, it’s just no longer enough.
The next generation of enterprise security is built on a different foundation: Zero Assumption. Because in a world where attackers log in instead of break in, the only safe assumption is that nothing is safe. Not the login, not the session, and definitely not the network.